In the last several years, IT asset management (ITAM) has become an increasingly vital topic—a way for companies to know, assess, and manage all the assets they own and use. Asset management can be a complicated topic: it is one of both depth and breadth, so subsets have emerged, including hardware asset management and software asset management (SAM). In this article, we will explore how SAM differentiates from ITAM and why it is a distinct discipline.
Defining ITAM and SAM
Let’s begin with defining the terms ITAM and SAM. Since IT service management (ITSM) frameworks are adopted in various organizational and technology context, several definitions exist across businesses and governing institutions. Consider the widely-accepted definitions by ITIL® and Gartner:
- IT asset management “provides an accurate account of technology asset lifecycle costs and risks to maximize the business value of technology strategy, architecture, funding, contractual and sourcing decisions.”
- Software asset management includes “all of the infrastructure and processes necessary for the effective management, control, and protection of the software assets within an organization throughout all stages of the lifecycle.”
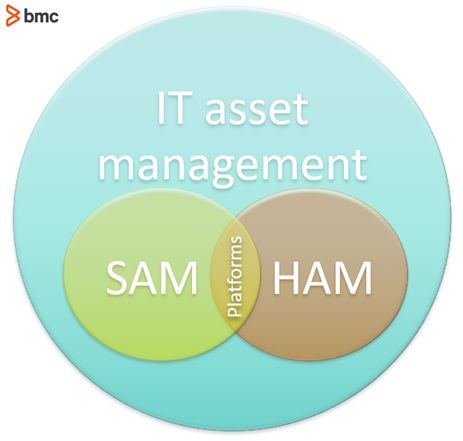
This graphic shows ITAM as an overarching discipline, with some subsets including SAM, hardware asset management (HAM), and the platforms that manage these processes.
Understanding ITAM
Asset management helps organizations manage the cost, risks, and opportunities of complex technology systems—by first establishing a ‘single source of truth’ amidst significant IT complexities such as on-prem and cloud software, rapid growth of IoT and BYOD, and seemingly never-ending audits, both internal and external. All this to say: IT assets have never been so complex, varied, or numerous. Any lack of visibility or control into your infrastructure is a sure-fire way to stop your digital transformation before it starts.
Even companies who excel at ITIL implementation are often lagging in their ITAM efforts. Many frameworks didn’t recognize the importance until recently: asset management wasn’t included until ITILv3, and COBIT 5, released in 2012, also focuses significantly on asset management. This ITAM lag may also be explained by increasingly complex configurations, which leave companies at odds on how to manage these multiplying assets.
No matter why you’re behind on your ITAM, you’ll want to prioritize this effort. Benefits of ITAM include:
- Routinely and easily assess strengths and weaknesses across a variety of benchmarked use cases, such as information security. These weaknesses offer a roadmap for business (thus IT) priorities.
- Improve your cost management holistically, now that you know which assets are using the most resources.
- Showcase the strides you’ve made within ITAM. You’ll get wider company buy-in once you’ve succeeded with smaller asset management projects.
- Understand your competition. Aligning with a widely-accepted ITAM strategy, like ITIL or COBIT, means you can compare your processes with others in the industry.
Understanding SAM, a subset of ITAM
In this era of DevOps, software assets present new requirements and challenges, especially when IT must rapidly provision a range of new solutions while keeping track of licensing, updates, and cost controls. As a result, the separate function of SAM has emerged within ITAM to deal specifically with software assets.
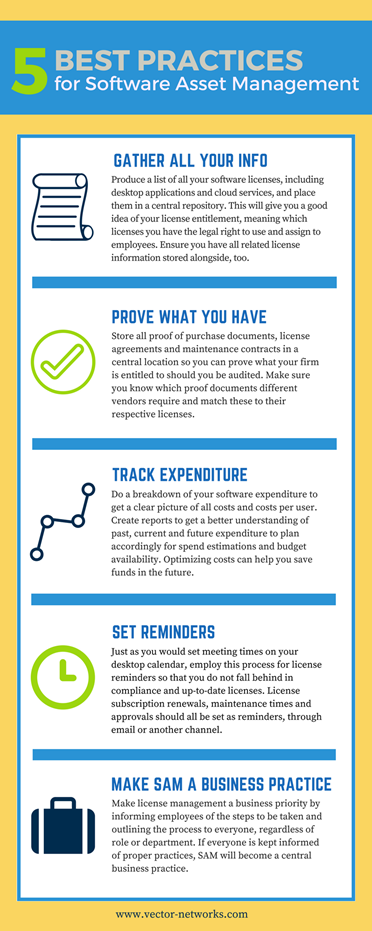
At a high level, SAM is an inventory management of software assets. Activities within a SAM framework include the accurate discovery, tracking, and management of licenses, costs, and risks associated with software assets. A good SAM function will align with ITIL or other ITSM processes in order to ensure effective IT service experience for end-users aligned with organizational goals.
Software assets are vastly different from hardware technologies. These characteristics define how software solutions are provisioned, utilized, and retired. IT teams can use SAM successfully to set realistic expectations, identify an asset management roadmap, and perform due diligence in these categories:
- Rapid provisioning. In DevOps and Agile environments, end users expect IT to provide an ever-expanding range of software solutions conveniently accessible via cloud. This complexity makes it challenging to establish a single source of truth. For example, inadequate asset tracking means your requested license count can easily exceed utilization requirements or go unaccounted in finance reporting.
- Cloud computing and shadow IT. Cloud computing enables users and individual departments to subscribe to new services and licenses. However, without an adequate IT governance policy to facilitate rapid cloud software provisioning, organizations run the risk of shadow IT. This “loophole” means that end users can adopt cloud solutions outside of the visibility, controls, and governance of your organization.
- Outsourcing. Partnerships are vital for successful digital transformation projects, yet these partnerships require management. Partner management should include:
- Addressing the impact of licensing
- Predicting and mitigating data security issues that arise when working with external organizations
- Considering the shared responsibilities across all partnerships
- Cybersecurity. Unlike traditional software assets, organizations employing cloud solutions have limited control and visibility into the technologies, underlying infrastructure, and off-premise data processing. That means cybersecurity tasks are harder to manage, but no less—perhaps more so—important than in traditional software environments. Cybersecurity management tasks include:
- Workforce education and awareness
- Vulnerability assessment
- Zero-day exploit patching
- Data-driven compliance. Software-based business processes are inherently data-driven, so it’s essential to understand how policies and processes are (not) satisfying data security requirements. Especially for organizations operating globally, a diverse set of compliance regulations is necessary to manage how data assets are accessed, transferred, processed, and controlled across multiple software assets.
Maturity assessment is key to evaluating present functional capabilities of the organization, before investing in appropriate tools. The next step will be to establish a process with respect to the data available regarding software asset deployment, utilization, and other stages of the asset lifecycle. Finally, continuous process improvement must be realized through monitoring and lifecycle assessment.
Convergence of ITAM components
As the above ITAM graphic illustrates, SAM independently addresses the management of software assets. For effective and holistic ITAM, however, integration with hardware asset management activities is critical. The disciplines overlap due to the inherent dependencies between hardware and software.
For example, the operating system and software solutions must be managed with respect to the hardware of laptops and workstations. The firmware on network infrastructure, such as routers and switches, must be updated and configured based on limitations and performance of the underlying hardware.
More importantly, technology requirements associated with hardware assets are now being addressed as software services. Organizations employ cloud infrastructure resources instead of deploying the hardware on-premise. The hardware, platform, and software operated in such environments are managed collectively. Even though the same SAM and ITAM solution may not suffice in managing all of these assets, organizations are increasingly opting for unified tools instead of stand-alone solutions to manage ITAM, SAM, cloud application management (CAM) and HAM activities separately.
ITAM and ITSM processes are tightly connected. Organizations need to make informed decisions about their IT assets in satisfying service management principles. Information related to asset compliance, risk and cost can be useful in satisfying the service management related to software performance and end-user experience. Other ITSM processes such as management of configuration items, security, service capacity and risk are also closely related with ITAM, and the SAM component is increasingly emerging as a focal point for these activities.
Choosing ITAM software
For top-of-the-line ITAM software, consider BMC Helix Discovery. Our cloud-native discovery and mapping solution offers the visibility companies need for effective and successful IT asset and software management. With out-of-the-box patterns, continuous updates, and discovery-as-code, your company can secure what you have, detect vulnerabilities, and see a full ROI within a year. Learn more on our BMC Helix Discovery datasheet.
Additional resources