If cloud growth in 2021 must be summed up in a single stat, it’s this: Gartner predicts that the worldwide public cloud revenue will grow by 23% in 2021 for a total revenue close to $332.2 billion U.S., up from $270 billion from last year.
Of course, there is much more nuance in cloud growth, especially since so many businesses and organizations around the world have adopted the work from home model, which relies heavily on web-based public cloud services.
Tracking cloud growth isn’t easy: does cloud mean the few companies that actually provide and drive the cloud—the cloud service providers? Or the thousands more companies that run services on those clouds—the IaaS, SaaS, PaaS providers?
Luckily, there are a few ways to estimate, measure, and predict cloud growth. In this article, we’ll round up the most important cloud growth storylines in 2021 by looking at:
- As a service revenue forecasts
- Cloud industry trends
- Positioning and spend among the big cloud providers
- Investment trends
As a service revenue in 2021-2022
“As a service” offerings are the easiest ways for organizations to get involved in the cloud. Software as a service (SaaS) is the most successful of these by far in the first decade of true cloud services as it’s forecasted to reach $122.6 billion by the end of this year. SaaS is all the services and software you run online, trading CapEx license spending for OpEx subscription costs.
(Deep dive into SaaS growth stats & trends.)
But SaaS is not the only player in cloud services. PaaS and IaaS were both big players, and now we’re seeing newer entries, like desktop as a service. In percentage terms, DaaS will see the highest growth at 67.7% followed by Infrastructure as a Service (IaaS) at 38.5%.
Gartner is a leading technology analyst firm who tracks U.S. and worldwide spending of a variety of technology. This recent chart indicates six leading as a service tracks and their forecast revenue. Their most recent research forecasts six key types of cloud services, which we’ll look at in depth below the table:
- BPaaS: Business Process as a Service
- PaaS: Platform as a Service (aka cloud application infrastructure services)
- SaaS: Software as a Service
- Cloud Management and Security Services
- IaaS: Infrastructure as a Service
- DaaS: Desktop as a Service
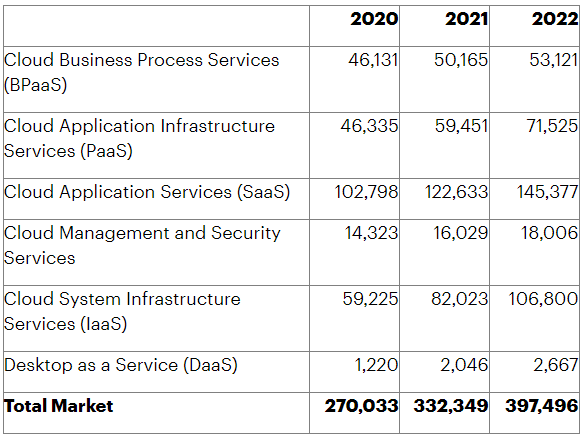
Worldwide public cloud services: end-user spending forecast (Millions of U.S. Dollars) (Source)
BPaaS: Business process as a service
Of the six cloud categories Gartner tracks, BPaaS is one of the smallest players, with its growth barely budging over the next few years, especially relative to the other categories. The market is still emerging and the growth trends are linear instead of the exponential rise seen in some of the ‘as a Service’ offerings.
This is because a significant proportion of BPaaS customers include SMB organizations with lower requirements on cloud business process services.
(Explore related BPMaaS offerings.)
PaaS: Platform as a service (aka cloud application infrastructure services)
The cloud application and infrastructure services will grow experience significant growth between 2020 and 2021, moving up to a solid third place among these six cloud categories. This growth is expected as more organizations migrate their IT workloads to the cloud. The growth rate is projected to increase at a lower rate between the years 2021-2022.
SaaS: Software as a service
Here is the big growth we expect of the cloud in terms of spending: the public cloud services market will continue to dominate the IT services industry owing to the proliferation of low-cost SaaS solutions that draw workers away from pricey on-prem software licenses.
Gartner predicts that the SaaS cloud application services market will consistently constitute at least one-third of the total public cloud revenue share for the next four years:
- In 2021 alone, the SaaS market will likely reach over $123 billion in revenue.
- By end of 2022, the growth rate increase even further, expecting to reach $145 billion in revenue.
Cloud management & security services
Cloud management and security services is the next category. Though it’s a smaller player, it’s growth is solid, nearly 30% growth from 2020 to 2022.
IaaS: Infrastructure as a service
IaaS was one of the original ‘as a Service’ opportunities, but one that didn’t live up to its early hype. Now, that’s changed. Industry experts see IaaS as the up-and-coming cloud solution that will eventually surpass SaaS in revenue. Gartner clearly agrees with this assessment, estimated IaaS revenue to almost double in between 2020-2022: up from around $60 billion to $110 billion in revenue.
Still, organizations have been slower to adapt IaaS, reportedly due to a skills gap on cloud migration strategies. The sheer quantity of migration strategies that take the past of least resistance—the lift and shift approach—indicate many organizations are ill-staffed to handle activities vital to true cloud optimization, such as:
DaaS: Desktop as a Service
In terms of raw growth, Gartner predicts DaaS will win out in the next years. This estimate is based on the surge in remote workers, as we noted in our State of ITSM report, which requires secure access to enterprise apps across devices and geographic regions.
However, the percentage growth doesn’t necessarily outweigh other as-a-Service offerings in terms of dollar increase: the project revenue change between 2020-2022 is $1.2 billion to $2.67 billion.
Overall Gartner predictions for the cloud
When it comes to security, Gartner’s forecast highlights the shifting focus toward cloud solutions to run mission-critical security and performance sensitive IT workloads. The cloud industry is proving that on-premises data center deployments don’t automatically translate into strong security. Today, in many situations, cloud computing is a secure alternative.
Similarly, foregoing some proportion of visibility and control into third-party cloud infrastructure doesn’t compromise the security posture considering the stringent compliance regulations and sophisticated security capabilities designed to protect customer data in the cloud.
For IaaS and PaaS use cases, where organizations are ultimately responsible for managing and securing their own IT workloads, the growth in cloud management and security services market suggests that the industry is responding with effective solutions that help organizations maximize the value potential of their public cloud investments.
This might be the biggest takeaway: The combined market share of IaaS and PaaS revenue will finally surpass the powerful SaaS market revenue.
Interesting cloud growth trends & stats
Surveys by a variety of research organizations point to a common trend: the combined spending of SaaS, PaaS, and IaaS models is growing exponentially.
Organizations are increasingly opting for multi-cloud environments that take advantage of all three cloud models, on-premise and off-premise. In fact, a majority of industry verticals average more than 10 cloud vendor subscriptions at every organization.
Let’s look at some of the interesting cloud growth trends expected in 2021 and beyond:
- 81% of all organizations have already adopted a multi-cloud strategy. 84% describe existing IT infrastructure as some form of a multi-cloud environment.
- 67% of the organizations operate cloud-based infrastructure environments
- AWS maintains the largest market share at 32%
- By the end of 2022, the US will have leapfrogged all other countries in terms of cloud adoption—by several years!
- Manufacturing ($19.7 billion), professional services ($18.1 billion), and banking ($16.7 billion) are the leading industry verticals in terms of public cloud spending.
- SaaS will remain the leading choice of cloud service model over the next few years, reaching $697 billion at a Compound Annual Growth Rate (CAGR) of 19%.
Trends in the Big 3 cloud providers
The next category to look at for cloud growth trends are the cloud providers themselves. The majority of as a service offerings run on someone else’s cloud, no matter if they’re a brand-new startup or a global enterprise. Here’s how the projected market share looks like:
- Amazon AWS: 32%
- Microsoft Azure: 18%
- Google Cloud: 8%
- IBM Cloud: 5%
- Alibaba Cloud: 5%
In terms of consumer cloud consumption trends:
- Google Drive: 94%
- DropBox: 64%
- OneDrive: 39%
- iCloud: 38%
(Read our comparison of the Big 3 cloud providers.)
Investment trends in the cloud industry
Increased adoption in cloud computing is driving investments in cloud computing startups and high-profile tech IPOs.
Top cloud IPOs
In terms of the service delivery model, web-based consumer apps and enterprise IT solutions can be considered as a SaaS offering. The service is hosted in third-party datacenters and delivered over the Internet on a subscription-based pricing model. The technology and business model characterizing high scalability and innovation has driven investor interest, particularly in the cloud infrastructure services segment that is a necessary enabler to all SaaS solutions in the consumer and enterprise IT markets.
Let’s highlight some of the top cloud infrastructure and data solutions IPOs:
- Asana, an enterprise productivity SaaS solution, IPO’d at $19 billion in September 2020.
- Snowflake, a data warehousing company IPO’d at $33.2 billion and is recently valued at $96 billion.
- SentinelOne, cybersecurity solutions provider IPO’d at $10 billion in June 2021—the highest ever cybersecurity IPO ever. As of September 2021, it is valued at over $16 billion.
- Confluent, a data-streaming platform company IPO’d at $11.4 billion in June 2021 and is currently valued at around $17 billion.
Data center trends
Another important part of the cloud services industry is the growing data center infrastructure segment.
Data center assets are critical for the sustained growth of public cloud service organizations. Datacenter organizations are pivotal to the growth of the economy as a variety of industry verticals are directly involved and affected by investments into datacenter organizations—construction, manufacturing, transportation, energy, scientific research, and more.
Let’s highlight some of the interesting datacenter investment trends as noted in the latest Frost & Sullivan research report:
- Datacenter industry is growing at a CAGR of 9.9%, from $244.74 billion in 2019 to $432 billion in 2025.
- The APAC region is leading the spending charts, replacing the North America region now at second, followed by EMEA at third. Emerging markets such as Southeast Asia are still at a “nascent stage” as compared to the Nordic region and the US.
Consumption of datacenter resources can also be measured in terms of power consumption and environmental impact. According to research:
- Datacenter facilities consume 3% of the global energy consumption and is soon expected to reach 8% mark.
- In terms of energy units, the increase will be from 292 TWh in 2016 to 353 TWh in 2030.
All these stats and trends verify and validate the exponential growth of the cloud computing industry. Cloud vendors, service providers and startup firms are gaining exponentially rising interest and popularity among investors, businesses and consumers.
Cloud (sub-)optimization stats
However, the growth figures should be viewed with the following caveat: cloud computing resources are drastically oversubscribed, underutilized and therefore, wasted. Take a look at the following research trends:
- On average, 30% of all organizations waste cloud resources and,
- 23% over budget for the cloud spending.
- 61% of the organizations consider cloud spending optimization as their top initiative for the fifth year in a row.
While all of these trends present cloud computing as essential to running a successful technology-driven business organization, the returns on cloud investments are still subject to a few critical challenges: successful cloud migration, cybersecurity, cloud resource optimization, people and change management, and long-term vision for cloud-enabled digital transformation.
Drivers of cloud growth
As we’ve shown in this article, cloud growth shows no signs of stopping. What are the key drivers of cloud growth? Certainly, the ease and startup works for many small businesses—especially brand new businesses that need affordable, scalable solutions.
We’d be remiss not to mention how the global pandemic has upended traditional economic growth and employee work models. The cloud has been essential to companies pivoting to work from home structures.
Other drivers, though, are awareness and openness to new ways of working. In the US, we’ve been following the ongoing saga of which cloud provider will service the Department of Defense cloud migrations.
Related reading
- BMC Multi-Cloud Blog
- Common Roles in Cloud Computing
- 10 Best Practices to Avoid Cloud Vendor Lock-In
- AR Cloud: The Augmented Reality Cloud
These postings are my own and do not necessarily represent BMC's position, strategies, or opinion.
See an error or have a suggestion? Please let us know by emailing [email protected].





